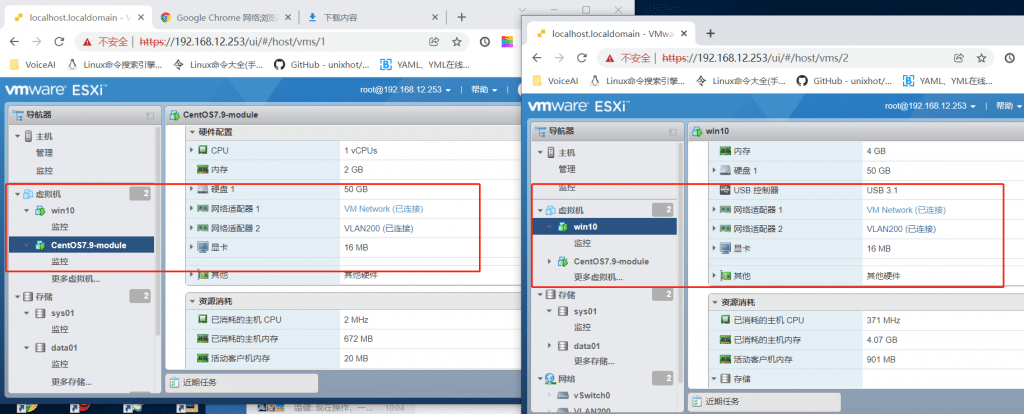
My colleague configured two network interfaces with different subnets on CentOS 7 Server, one network interface was subnet 192.168.12.0/24, another was 192.168.200.0/24. Only subnet 192.168.12.0/24 could be reachable. if disabled one network interface, another was working immediately. He tested on Windows 10 with the same subnets, both network interfaces was working well and was able to be pinged.
Let’s put the solution here.
To use temporarily
sysctl -w net.ipv4.conf.all.rp_filter=2To make this change persistent across reboots. add to the /etc/sysctl.conf file.
echo net.ipv4.conf.all.rp_filter=2 >> /etc/sysctl.confRoot Cause
RHEL 6 and above defaults to using Strict Reverse Path Forwarding filtering. As CentOS is quite similar to RHEL, it applies to the CentOS series as well.
What is Reverse Path Forwarding
Reverse Path Forwarding is used to prevent packets that arrived via one interface from leaving via a different interface. when outgoing routes and incoming routes are different, it is sometimes referred to as asymmetric routing. Routers often route packets this way, but most hosts should not need to do this. Exceptions are some applications that need to send traffic out over one link and receive traffic over another link. if no special requirement, it is best enabled as it prevents users spoofing of IP addresses and reduces DDoS attacks.
Reverse Path Forwarding has three options.
0 – No source validation
1 – Strict mode, if the incoming interface is not the best reverse path, the packet check will fail, the failed packets are discarded.
2 – Loose mode, the packet is dropped only if the source address is not reachable via any interface.
Summary
It is advised by RedHat that the best way for the function is to leave it enabled if you have no requirements. Reverse Path Forwarding is also used in routers. for more information about RPF, you can check RedHat Document and RFC 3704.