As Kubernetes is deprecating docker as container runtime after version 1.20, we decided to choose Containerd as our Kubernetes runtime. Our Kubernetes cluster is running on the Aliyun Cloud, with 3 master nodes and 6 worker nodes.
This post documented how to configure a private repository in Containerd. compared with Docker, I feel that client tools like crlctl is not powerful as the Docker client.
Configure private repository
To configure image registries create/modify the /etc/containerd/config.toml as follows
[plugins."io.containerd.grpc.v1.cri".cni]
bin_dir = "/opt/cni/bin"
conf_dir = "/etc/cni/net.d"
max_conf_num = 1
[plugins."io.containerd.grpc.v1.cri".registry]
[plugins."io.containerd.grpc.v1.cri".registry.mirrors]
[plugins."io.containerd.grpc.v1.cri".registry.mirrors."docker.io"]
endpoint = ["https://registry-1.docker.io"]
[plugins."io.containerd.grpc.v1.cri".registry.mirrors."devhub.devops.xxx.com"]
endpoint = ["https://devhub.devops.xxx.com"]
[plugins."io.containerd.grpc.v1.cri".registry.configs]
[plugins."io.containerd.grpc.v1.cri".registry.configs."devhub.devops.xxx.com".auth]
username = "robot"
password = "5UPu2MVzC"
The endpoint is a list that can contain multiple image registry URLs split by commas.
The auth is the credentials that login
Restart contained to take effect
systemctl restart containerd
Verify
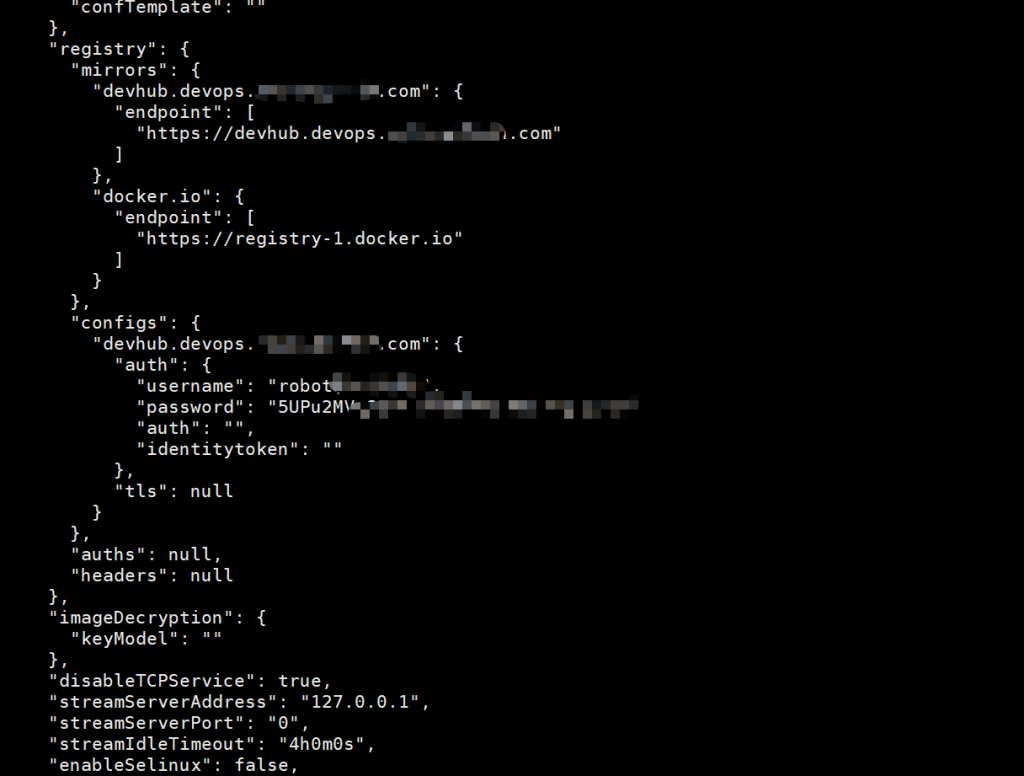
perform the command to check the configuration.
crlctl info
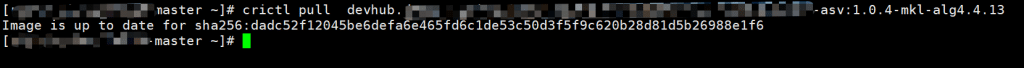
Pull Image
Summary
You will be able to know how to configure a private in Containerd and how to use client – crictl to pull images or do other actions. for a heavily-docker user, the client crictl is not friendly, especially pulling images. no idea it is pulling or is stuck there for network connection reason or other reasons.